CEOs: Maintain Cyber Resilience While Dealing with COVID-19

IT Engineer Holding Notebook and Walking Through Data Center Full of Working Rack Servers.
What is the relationship between the coronavirus outbreak and cybersecurity?
Answer: They both require conscious CEO leadership—and attending to one must not subtract from a focus on the other.
Attempting to “flatten the curve” of coronavirus diffusion by practicing “social distancing” has caused enormous business upheaval. Massively more people working from home combined with disrupting and modifying supply chains and routine work processes significantly increases the potential for cyber breaches against unprepared organizations. For example, rushing to set up thousands of new computers for remote work without adequate security policies and processes already in place opens enormous openings for penetration of corporate networks.
For a CEO not already exercising leadership to ensure that cyber risk is well managed, the current crisis is a wakeup call. While digitalization of business over the past two decades has delivered substantial improvements in efficiency, online cyber risk has mushroomed, growing to become the single greatest hazard to most businesses. The onus to protect the organization ultimately falls on its leader, the CEO. What can a CEO do to implement changes and mitigate the risk?
The crux of the problem is that many boards, C-suite executives, and CAEs [chief audit executives] have not yet caught up with the fundamental structural change digitalization digitalization implies.
Dominique Vincenti, Uber Chief Audit Executive
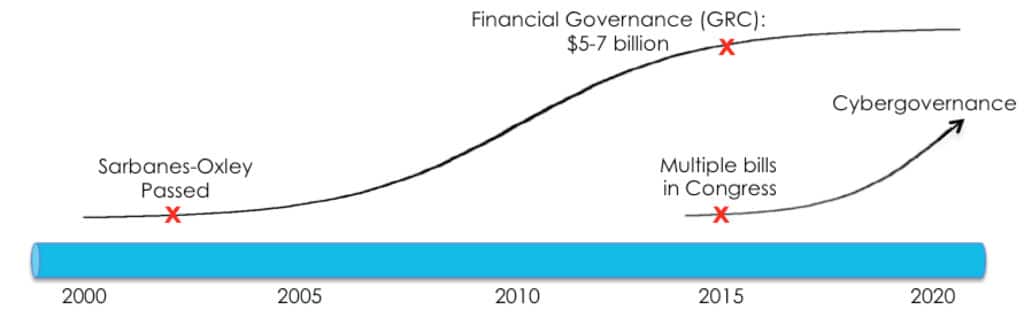
Dr. Michael Parent of Simon Frasier University recently pointed out that “cybersecurity has reached its Sarbanes-Oxley moment.” Several years ago, responses to cyber risk began mirroring steps previously taken to handle financial risk, and we began to hear about cybersecurity governance, or “cybergovernance” (see diagram below). In reaction to the out-of-control fraud exposed at Enron and other notorious companies, the Sarbanes-Oxley Act of 2002 mandated dramatic upgrades in financial reporting. Today, the accelerating threat from cyber risk demands analogous behavioral changes. These could come from farsighted, proactive CEOs—otherwise, Sarbanes-Oxley-like cyber legislation will likely be enacted.
| Sarbanes-Oxley | Cybergovernance | |
| Instigation | Rash of highly publicized frauds (e.g., Enron, WorldCom) | Rash of highly publicized breaches (e.g., JPMorgan Chase, Target) |
| Motivation | Restore loss of public and investor confidence due to financial scandal (INTERNAL THREAT) | Restore loss of public and investor confidence due to cyber breaches (EXTERNAL THREAT) |
| Challenge | Mitigate financial risk | Mitigate cybersecurity risk |
| Solution | Stricter financial governance laws | Stricter cybersecurity governance laws |
| Driver | Senate Banking Committee | SEC, FTC, FINRA, CFPB |
| Outcome | Sarbanes-Oxley Act (2002) | 11 bills currently in Congress |
Change Starts with the CEO
For the past five years, boards and executives have been told repeatedly that responsibility for managing cyber risk must start at the top. Two-thirds or more of recorded cyber breaches are not caused by failing technology but instead by failures of people, policy, and process.1 The obvious response is to implement an effective cyber risk governance program that helps executives and board oversee cyber risk just as they do other enterprise risks, without requiring them to become cyber experts.
Recently, members of the Chinese military were charged with stealing names, addresses, Social Security and driver’s license numbers, and other personal information stored in Equifax’s databases. Access to massive amounts of personal data was possible because software patches weren’t applied in a timely manner. Equifax’s CEO blamed an employee, but the facts pointed to management’s failure to ensure that policies and processes were followed, which subsequently led to massive third-party lawsuits alleging negligence and malfeasance by the management and the board.2
Despite high-profile management failures and repeated warnings to CEOs, the frequency and impact of cyber events, especially against small and medium businesses, continues to accelerate. As Scott Steinberg of CNBC recently noted, “With 43 percent of online attacks now aimed at small businesses, a favorite target of high-tech villains, yet only 14 percent prepared to defend themselves, owners increasingly need to start making high-tech security a top priority.”
Small and Medium Enterprise Risk
To identify the causes and effects of cyberattacks on small and medium-sized businesses in North America and Europe, property and casualty insurer Hiscox recently surveyed 3,300 firms. The study revealed that more than half of companies in the United States had suffered a breach within the previous 12 months, and 40 percent had incurred multiple breaches. Even worse, the estimated total losses had doubled those of the previous year. The percentage of medium-sized firms with between 50 and 249 employees reporting recent cyber incidents jumped from 36 percent the previous year to 63 percent.
Despite increased regulation and a number of high-profile breaches, firms actually achieved lower scores in our cyber readiness model this year, with nearly three quarters (74%) failing to reach our threshold for expertise in any area.
Hiscox Cyber Readiness Report 2019
Growing Awareness
Given the increased attention to and spending on cybersecurity, is progress being made? With respect to growing awareness of the problem, the answer is yes. The Institute of Internal Auditors recently published its inaugural OnRisk report. The report asked participants to list and rank the greatest risks their organization faces in 2020 and is expected to face in 2024. Cybersecurity and data protection were number one in both cases.
If awareness has grown, why do so few CEOs apply the energy and resources needed to implement an effective cyber risk program? It’s not really a mystery, and it comes down to the positive orientation of most leaders. As Robert S. Kaplan and Anette Mikes write in Harvard Business Review, “Managing risk is very different from managing strategy. Risk management focuses on the negative—threats and failures rather than opportunities and successes. It runs exactly counter to the ‘can do’ culture most leadership teams try to foster when implementing strategy. And many leaders have a tendency to discount the future; they’re reluctant to spend time and money now to avoid an uncertain future problem that might occur down the road, on someone else’s watch.”
Changing Mentality
Most larger companies have begun treating cybersecurity as an enterprise risk alongside financial and other risks. As cyber risk threatens to impact credit ratings that determine access to needed capital, small and medium-sized companies must invest in policies and processes that will increase their cyber resilience.
Managing cyber risk effectively requires applying a set of management principles and taking direct steps in support of them. I suggest applying five principles derived from studying the Equifax breach that will increase your company’s cyber resilience:
- Move immediately when action is needed. Stock index evaluator MCSI presented the results of its evaluation to Equifax management almost a year before its massive breach. Despite Equifax receiving a score of zero out of 10 in MCSI’s cyber assessment, management failed to ensure that basic measures were in place before the breach occurred (for example, a process to double-check that patches were being regularly applied). Begin investing now to put the 3 P’s of good cyber governance—People, Policy, Process—in place to increase cyber resilience.
- Learn from the mistakes of others. When you see a headline about a breach, look for lessons and discuss them with your staff. For example, the Equifax breach exposed unacceptably negligent behavior and a lack of commitment to well-understood cyber policies and processes. One obvious first step is to implement policies and processes based on national standards—for example, the National Institute of Standards and Technology’s Cybersecurity Framework—that can bridge the gap between “tech speak” and “exec speak” so your board and management team can track progress.
- Apply the same rigor to cyber audits that you do to financial audits. Well-accepted standards become the foundation for rigorous cyber auditing. Automating continual tracking of improvements leads to more efficient audits. Encourage staff members to capture their comments and electronic artifacts that support their input as they complete self-assessments, information that will provide valuable input to those who may audit the assessments. If you have an internal audit group, task them with auditing the organization’s progress toward greater resilience, or consider hiring an outside auditor.
- Engage all key stakeholders. Having strong IT and Security teams is important, yet many other stakeholders need to do their part. For example, Human Resources and Purchasing departments create cyber risk when they bring in new people and technologies. Educating them about their cybersecurity responsibilities and arming them with protective policies and processes is vital to the success of your cyber risk management program. The CEO can help IT and Security by creating an inclusive cyber culture that helps all relevant stakeholders—for example, HR, Purchasing, Internal Audit, General Counsel, and Risk Management—understand what they bring to the table and incorporate practices that protect the organization.
- Improve continuously. Standing still in the face of continuously changing cyber threats means falling behind. Establish a program that monitors and reports continuous improvements. As mentioned previously, the National Institute and Standards and Technology brought 3,000 experts from commerce, government, and academia together to create its comprehensive Cybersecurity Framework. While every organization is unique, you can take advantage of the massive amount of experience embedded in leading frameworks when building your program.
The Bottom Line
The increased cyber risk caused by a disruption like the coronavirus event is a threat, yet it’s also an opportunity to reexamine cyber risk management policies and processes, which few CEOs feel confident about managing. When confronting the existential risk posed by a massive cyberattack, they are naturally more comfortable focusing on growing revenue.
Moving past this tension to include regular discussions of cyber risk in business reviews is challenging. The CEO should lead by emphasizing the significance of effective cyber risk management to the company’s digital transformation, and by encouraging incorporation of appropriate behavioral changes into normal operations. Cyber risk will remain long after the coronavirus pandemic has come and gone, and continuing CEO leadership is essential.
Most people haven’t heard of the SAFETY Act. Soon after 9/11, the SAFETY Act was passed to encourage development of solutions that protect the homeland. This federal law offered liability protections to firms creating anti-terrorism products and services, since the high risk could otherwise discourage their development. For example, the software that powers the Transportation Safety Administration’s Secure Flight program was built by Infoglide, a small firm in Austin. Imagine the liability if the software allowed a bad actor to board a plane that was later attacked.
Lawsuits against the federal government are prohibited. The SAFETY Act extends this “sovereign immunity” to offerings vetted and approved by the Department of Homeland Security (DHS). Companies that use these offerings, designated as “Qualified Anti-Terrorism Technology” by DHS, gain significant liability from third-party lawsuits against their boards and executives that allege negligence.
It’s time that business leaders begin to accept that cybersecurity, rather than being a technology problem, is another form of enterprise risk analogous to financial risk, and that the responsibility for it falls on their shoulders.
“Equifax: Cyber Law Test Case of the Century,” West Law Journal
- “A New Metric for Cybersecurity,” Editor’s Note, Corporate Board Member, Second Quarter 2018, Volume 21, Number 2, p. 2.
- Bob Barker, “Equifax: The Cyber Law Test Case of the Century,” Westlaw Journal, Volume 32, Issue 5, January 2018.